Ask Malware What
It Really Does.
AI-powered malware analysis in fully interactive multi-OS sandboxes. Detonate, observe, and understand threats — guided by an AI co-pilot.
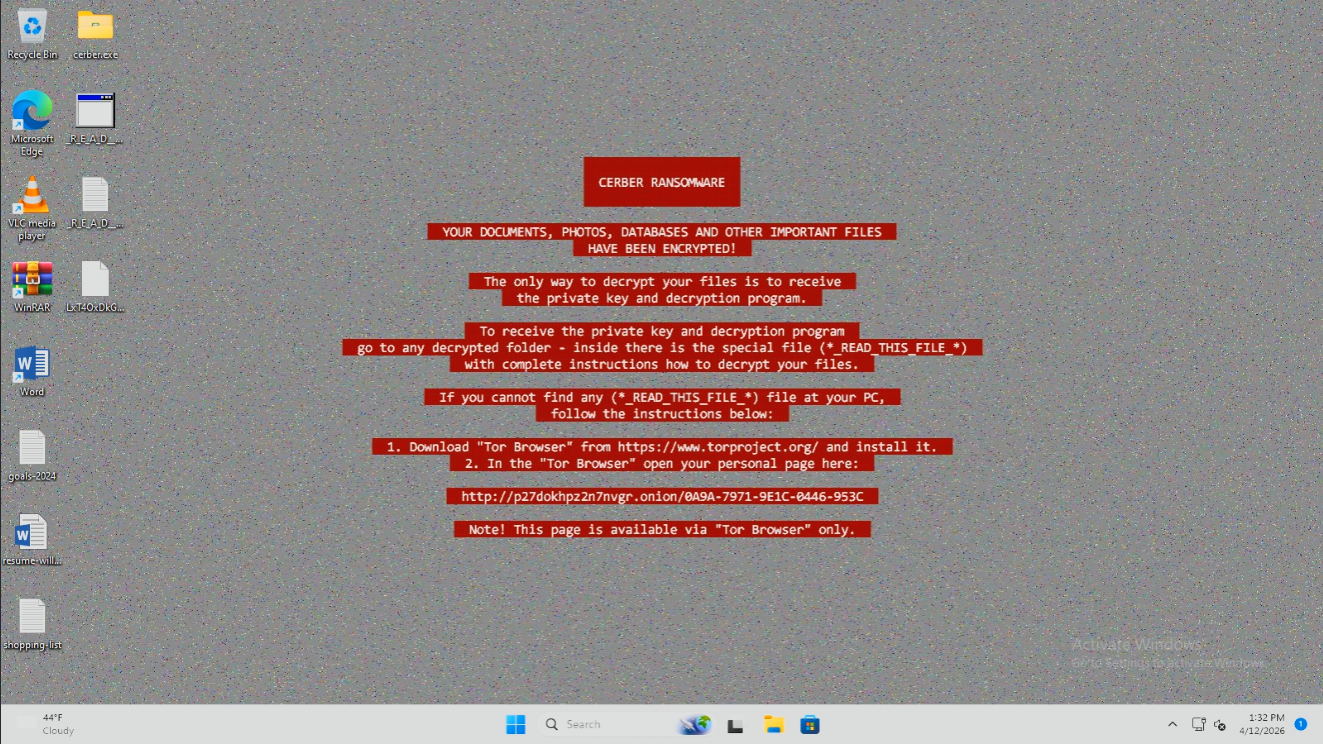
See Retrace detonate and dissect a real ransomware sample in 2 minutes.


2026.pdf.exe
.locked
.locked
.locked
.locked
Analyze malware in a safe environment.
Every sample fires inside a disposable VM your laptop never touches. Watch every artifact unfold in real time, interact with the detonation live, and walk away with a verdict + IOCs your SOC can ship today.
0000000000000000000000000000000000000000000000000000000000000000Now ask it anything.
The sandbox already captured every byte. The AI reads that trace — every event, every technique, every artifact — and answers in real analyst language. Every claim comes with receipts. Nothing is invented.
Grounded in the trace
Every claim cites a specific event, technique, or captured file. No LLM hallucination — the AI only speaks about what the sandbox actually observed.
Your sandbox's memory
Pattern-matches against every detonation you've ever run. Your LockBit samples teach it what LockBit looks like in your environment — not a generic model.
SOC-ready briefings
Export answers as Markdown, PDF, or STIX 2.1 bundles for your MISP or TIP. Chat transcripts go in, artifacts ready for ingest come out.
Your data stays yours
Inference runs on-prem for Enterprise and fully air-gapped for Sovereign deployments. No sample bytes, no IOCs, no tool calls ever leave your infrastructure.
Deploy your way.
From individual researchers to air-gapped defense networks.